OAuth phishing attacks are a rising threat in the realm of cybersecurity, exploiting vulnerabilities in the OAuth authentication protocol to deceive users and compromise their sensitive information. Cybercriminals have become increasingly sophisticated, using seemingly legitimate emails that impersonate trusted identity providers like Microsoft Entra ID and Google Workspace. These phishing emails often contain links that lead to malicious OAuth applications, redirecting victims to harmful environments under the guise of safe and recognized domains. As attackers utilize the inherent functionality of OAuth to seamlessly lead users down dangerous paths, the importance of cybersecurity awareness has never been more critical. Understanding the tactics of identity provider fraud helps individuals and organizations protect themselves from becoming unwitting targets in this evolving landscape of cyber threats.
Phishing schemes leveraging OAuth protocols represent a significant challenge in online security, manifesting as subtle yet effective manipulations aimed at unsuspecting users. In these attacks, perpetrators craft deceptive emails that appear to originate from reputable sources, making it easy for victims to fall into the trap. This form of identity theft often utilizes false authentication requests that masquerade as urgent communication, leading individuals to inadvertently share their credentials with malicious entities. As organizations grapple with the influx of these tactics, it becomes imperative to enhance cybersecurity measures and raise awareness about potential vulnerabilities. The continuous evolution of malicious strategies underscores the need for vigilance against modern phishing techniques.
Understanding OAuth Phishing Attacks
OAuth phishing attacks are a growing concern in the realm of cybersecurity, exploiting the very features designed to enhance user authentication on numerous platforms. Cybercriminals leverage the OAuth protocol’s inherent functionality that allows for legitimate link redirection to craft malicious emails that appear to originate from trustworthy identity providers such as Google and Microsoft. By embedding flawed URLs that seem safe but lead to harmful destinations, attackers can deceive users into unwittingly granting access to their accounts without realizing they are engaging with a phishing email. This practice signals a new era of identity exploitation, where the attackers mask their motives behind the guise of legitimate user interactions.
The nuances of OAuth phishing often go unnoticed, as traditional measures that advise users to hover over links are outdated in the current cyber landscape. Instead, organizations need to foster an environment of cybersecurity awareness that encourages employees to assess the context of any authentication request thoroughly. Users must be trained to recognize unexpected requests for access that do not align with their normal workflows, as OAuth phishing relies on manipulating these routine behaviors to capture sensitive information and compromise user accounts.
OAuth Authentication Vulnerabilities
OAuth authentication presents several vulnerabilities that cybercriminals can tactically exploit for phishing attacks. The misuse of OAuth’s built-in redirection features demonstrates how attackers can craft deceivingly convincing workflows that lure unsuspecting victims into credential disclosure. When an email carries a seemingly genuine OAuth link, it may take users through the authentic identity provider’s initial authentication, but the final landing page is usually controlled by the attackers. This process underscores the vulnerabilities present in the OAuth framework, where its legitimate uses can be twisted to serve nefarious purposes.
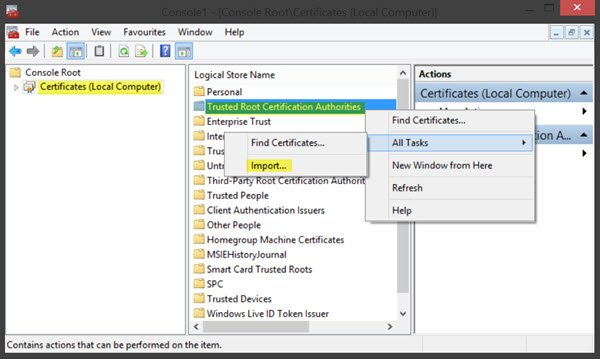
Moreover, the lack of stringent monitoring over registered OAuth applications presents a governance gap that allows these phishing schemes to thrive. Organizations often overlook the significance of managing application permissions and monitoring redirect URIs effectively. By allowing excessive privileges and broad consent settings, enterprises unintentionally open doors for attackers to exploit vulnerabilities in their identity governance. Continuous auditing and stringent consent management can significantly mitigate these vulnerabilities, minimizing the chances for misuse by potential threat actors.
The Role of Malicious OAuth Applications in Cyber Attacks
Malicious OAuth applications play a pivotal role in orchestrating phishing attacks that target unsuspecting users. These applications, often appearing as legitimate, can be designed to harvest user credentials by masquerading as necessary tools for business operations. When users unknowingly consent to the permissions requested by these malicious applications, they may inadvertently expose their sensitive information or fall victim to further exploits that leverage the initial compromise. The risk is compounded when organizations fail to monitor the scope and privileges of OAuth integrations, which can lead to unchecked access and data breaches.
Microsoft’s blog highlighted the existence of numerous threatening OAuth applications that had already been disabled due to their malicious nature. However, the continuous evolution of these threats indicates that attackers are relentlessly finding new strategies to bypass existing security measures. As enterprises increasingly rely on digital tools that utilize OAuth for authentication, awareness of how malicious applications can infiltrate the system is critical for safeguarding sensitive information from phishing and other cyber threats.
Building Cybersecurity Awareness Among Employees
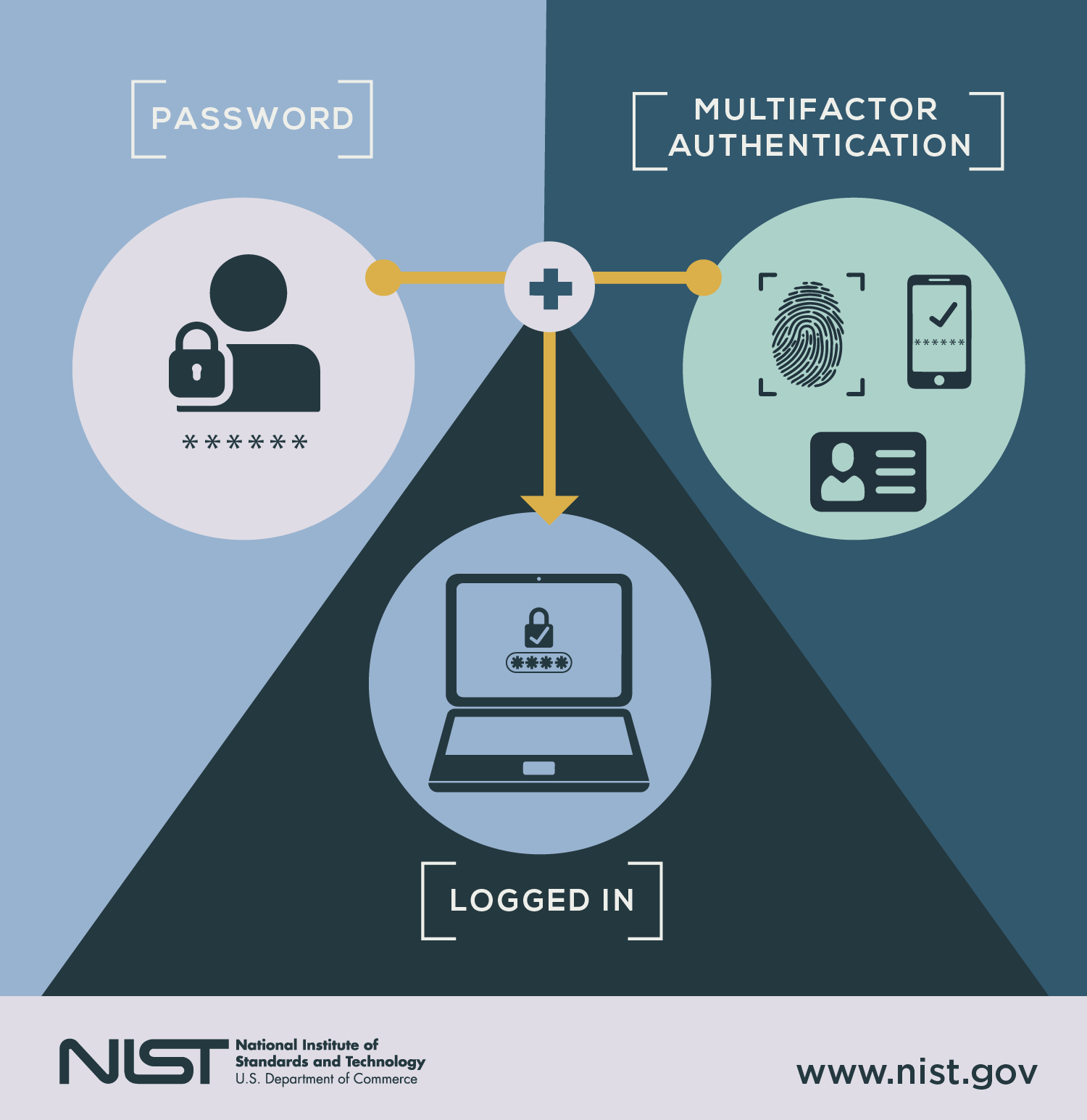
Cybersecurity awareness is vital in the defense against OAuth phishing attacks and other forms of identity fraud. Employees must be educated on recognizing potential threats in their digital communications, especially those involving authentication processes. By shifting the focus from merely checking links to validating requests and assessing context, organizations can significantly enhance their defenses against exploitative phishing attempts. Implementing regular training on the signs of phishing and the importance of secure authentication can empower employees to act as the first line of defense in maintaining cybersecurity.
Moreover, fostering an environment where employees feel comfortable reporting suspicious activities can lead to timely interventions that thwart potential breaches. Organizations should prioritize creating streamlined processes for reporting unexpected authentication requests or errors. Encouraging proactive engagement among employees regarding cybersecurity awareness can create a cohesive frontline defense against phishing attacks, ensuring a secure operational environment.
The Shift Towards Contextual Awareness
As phishing tactics evolve, especially with OAuth vulnerabilities, shifting the focus from simply scrutinizing URLs to a broader understanding of the context is paramount. Sakshi Grover underscores the need for organizations to recalibrate their cybersecurity training and awareness to emphasize context validation: recognizing if an authentication request aligns with expected business activities is vital. This proactive approach can mitigate risks, prompting employees to scrutinize not only the sender but also the relevance and timing of the request.
This transition reflects a fundamental change in how individuals assess risk in digital interactions. By instilling a habit of questioning the legitimacy of every authentication journey, organizations create a culture of skepticism towards unsolicited prompts. Such awareness can significantly reduce the chances of users falling victim to OAuth phishing and similar attacks that exploit the human element in cybersecurity. Awareness, coupled with robust security practices, equips employees to navigate the complex landscape of digital threats effectively.
Addressing the Governance Gap in OAuth Applications
The governance gap surrounding OAuth applications presents a critical vulnerability for organizations today. As enterprises increasingly rely on third-party applications for operational efficiency, the oversight of these applications has often fallen short. Broad consent settings and lax monitoring of redirect URIs create an inviting environment for attackers seeking to exploit weaknesses within the OAuth framework. Sanchit Vir Gogia emphasizes the importance of organizations reassessing their governance structures to ensure stringent compliance and oversight, especially given the rapid expansion of SaaS and cloud-based solutions.
Proactively managing OAuth applications includes conducting regular audits on application permissions and ensuring that only necessary applications maintain access. Implementing a robust governance strategy allows organizations to not only identify and mitigate potential threats but also to maintain a safe operational landscape. Continual vigilance and adjustment of access permissions, along with an acute understanding of each application’s necessity, help close the governance gap that fraudsters seek to exploit.
Combating Identity Provider Fraud
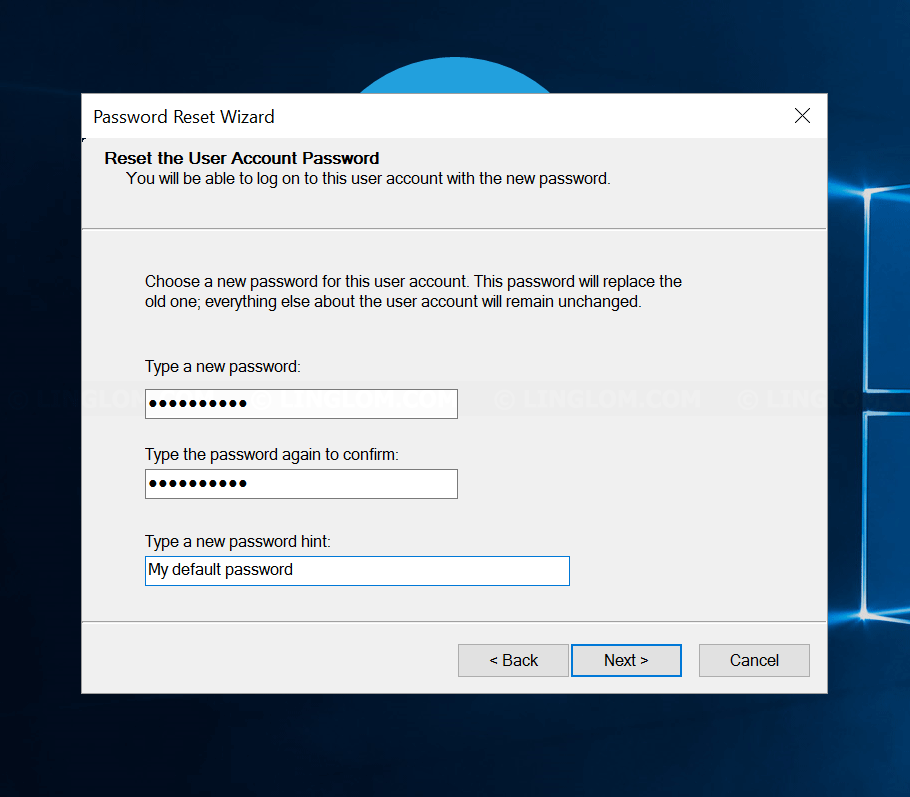
Identity provider fraud represents a serious threat within the digital landscape, especially as cybercriminals manipulate OAuth protocols to deceive users. With attackers impersonating legitimate services, recognizing fraudulent behavior requires enhanced vigilance and a clear understanding of the authentication processes involved. Organizations must reinforce their identity verification procedures by implementing multi-factor authentication (MFA) and real-time monitoring that flags unusual activities associated with known identity providers.
To combat identity provider fraud effectively, a proactive approach is necessary. Educating users about the risks associated with unsolicited authentication requests, along with actionable guidelines for verification, is crucial. Encouragement to report suspicious activity or unexpected redirects allows organizations to build a robust support system that can swiftly act against potential fraud. This layered security model not only protects individual users but also reinforces overall organizational cybersecurity.
Securing OAuth Workflows in Enterprise Applications
Securing OAuth workflows is essential as businesses increasingly integrate various applications to facilitate seamless operations. OAuth’s design, while beneficial for enabling third-party access, can also become a vector for cyber threats if not properly managed. To ensure security, enterprises must adopt a rigorous framework that includes regular assessments of all OAuth-related applications, carefully evaluating their permissions and access scopes.
Additionally, organizations should implement stringent policies governing the use of OAuth tokens and redirect URIs. Clear guidelines and protocols ensure that all employees understand the risks involved with granting access through OAuth, reinforcing the significance of only connecting with verified applications. This meticulous management of OAuth workflows enhances overall security postures and significantly reduces the likelihood of successful phishing attacks.
The Importance of Continuous Monitoring and Audits
Continuous monitoring and regular audits are critical components in the fight against OAuth phishing attacks. Cybersecurity threats are increasingly dynamic, and organizations must maintain a proactive stance on identifying and addressing vulnerabilities within their systems. By integrating automated monitoring solutions that track OAuth activities and permissions, businesses can detect unusual patterns that suggest malicious behavior and take immediate action to mitigate risks.
Furthermore, regular audits of registered OAuth applications ensure that only necessary and trusted applications have access to sensitive data. This practice not only safeguards information but also helps organizations eliminate unnecessary risks associated with unused or outdated applications. By combining thorough monitoring with comprehensive audits, enterprises can foster a resilient cybersecurity environment capable of adapting to evolving threats.
Frequently Asked Questions
What are OAuth phishing attacks and how do they work?
OAuth phishing attacks exploit the legitimate features of the OAuth authentication protocol to trick users into providing sensitive information. Attackers send phishing emails mimicking official communications, redirecting users to authorized URLs that appear to be legitimate while actually leading to malicious sites. This manipulation takes advantage of the trust placed in identity providers, making it crucial for users to thoroughly validate the context of any authentication requests.
How do phishing emails contribute to OAuth authentication vulnerabilities?
Phishing emails often entice users with fraudulent requests for password resets or e-signatures, embedding links that redirect to OAuth authorization endpoints. While these links may appear secure, attackers use flawed parameters to manipulate the OAuth workflow, ultimately redirecting victims to malicious sites. Users must be educated to recognize these phishing tactics to protect against OAuth authentication vulnerabilities.
What is identity provider fraud in the context of OAuth phishing attacks?
Identity provider fraud occurs when attackers impersonate legitimate identity providers using OAuth phishing techniques. Through this fraud, victims are presented with authentication screens that appear genuine, leading to unauthorized access to sensitive information. Understanding how attackers utilize trust in well-known identity providers is essential for users to recognize and avoid becoming victims of such tactics.
How can organizations defend against malicious OAuth applications in phishing attacks?
Organizations can defend against malicious OAuth applications by implementing strict governance of application registrations, regularly auditing app permissions, and limiting user consent for third-party applications. Educating employees about the risks associated with OAuth phishing attacks and encouraging vigilance in authentication contexts are also vital steps towards enhancing cybersecurity awareness.
What role does cybersecurity awareness play in preventing OAuth phishing attacks?
Cybersecurity awareness is crucial in mitigating OAuth phishing attacks. Employees must be trained to recognize phishing tactics, understand the importance of validating the context of authentication requests, and refrain from initiating login attempts from unsolicited links. Fostering a culture of cybersecurity vigilance helps individuals and organizations better avoid falling victim to these sophisticated phishing schemes.
What recommendations does Microsoft provide to mitigate OAuth phishing risks?
Microsoft recommends organizations restrict user consent to third-party OAuth applications, conduct regular audits of app permissions, and remove unused or overly privileged applications. Additionally, implementing effective training programs for employees about recognizing phishing tactics can significantly reduce the risks associated with OAuth-related attacks.
How do malicious OAuth applications operate in the context of cyber threats?
Malicious OAuth applications operate by exploiting the OAuth protocol’s inherent functionality, redirecting victims through trusted endpoints while ultimately leading them to malicious destinations. These applications are often registered with flawed parameters, allowing attackers to collect sensitive information such as login credentials and session cookies. Monitoring and managing OAuth applications are essential to prevent such cyber threats.
What are the implications of governance gaps in OAuth application management?
Governance gaps in OAuth application management can lead to critical vulnerabilities, as many organizations have not updated permissions or monitored redirect URIs sufficiently. This oversight allows attackers to manipulate registered applications and execute OAuth phishing attacks effectively. Organizations must prioritize improving governance maturity and ensuring regular oversight of OAuth applications to mitigate these risks.
| Key Point | Details |
|---|---|
| Purpose of Attack | Exploit OAuth redirection to lead users to malicious sites. |
| Attack Method | Phishing emails impersonating legitimate requests redirect victims to harmful destinations via manipulated OAuth links. |
| Unique Features | Attack utilizes real OAuth endpoints but fails under crafted parameters, leading to attacker-controlled URIs. |
| Red Flags | Traditional link checking is ineffective; context of requests is more critical. |
| Advice for Organizations | Restrict permissions for OAuth applications, perform audits, and ensure governance controls. |
Summary
OAuth phishing attacks are a growing threat, exploiting built-in features of the OAuth authentication protocol. Attackers craft phishing emails that redirect users to malicious sites while masquerading as legitimate identity provider links. Organizations must enhance their security awareness, focus on validating the context of authentication requests, and break complacency in application governance to mitigate the risks posed by these sophisticated attacks.